[Date Prev][Date Next][Thread Prev][Thread Next][Date Index][Thread Index]
Re: [Full-disclosure] FileZilla (client) public credentials vulnerability
- To: full-disclosure@xxxxxxxxxxxxxxxxx
- Subject: Re: [Full-disclosure] FileZilla (client) public credentials vulnerability
- From: Tobias Ulmer <tobiasu@xxxxxxxx>
- Date: Fri, 16 Sep 2005 20:13:53 +0200
PASTOR ADRIAN wrote:
> Title: FileZilla (client) public credentials vulnerability
> Risk: Medium
> Versions affected: <=2.2.15
> Credits: pagvac (Adrian Pastor)
> Date found: 10th September, 2005
> Homepage: www.ikwt.com www.adrianpv.com
> E-mail: m123303 [ - a t - ] richmond.ac.uk
>
[...]
> Regards,
> pagvac (Adrian Pastor)
> Earth, SOLAR SYSTEM
>
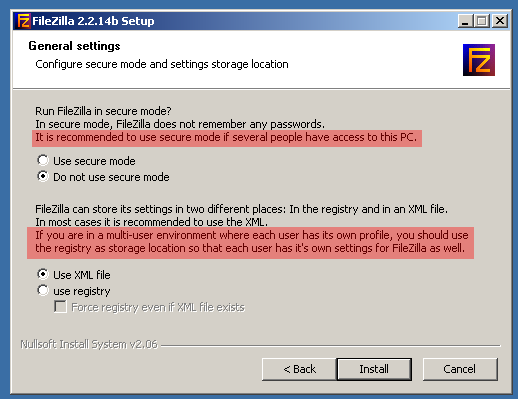
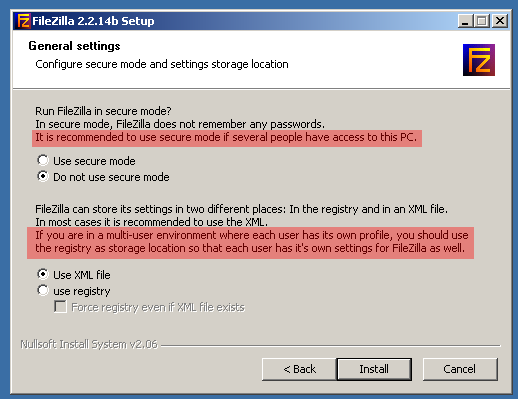
I don't know why I even reply... But anyway, I attached a screen shot
especially for you. Please read it.
a) FileZilla Users most probably are the only user of the computer. This
is why the default makes sense (They "work" as administrator anyways).
b) There is a "secure mode" witch prevents you from saving any password
at all witch is the best solution if you want to be on the safe side.
c) There is an option to save the settings in the registry and ignore
the xml file. Settings are stored in HKEY_CURRENT_USER witch is in fact
under X:\%homepath%\username\NTUSER.DAT and is protected by the
filesytem ACL.
Tobias
_______________________________________________
Full-Disclosure - We believe in it.
Charter: http://lists.grok.org.uk/full-disclosure-charter.html
Hosted and sponsored by Secunia - http://secunia.com/